// 2026
-
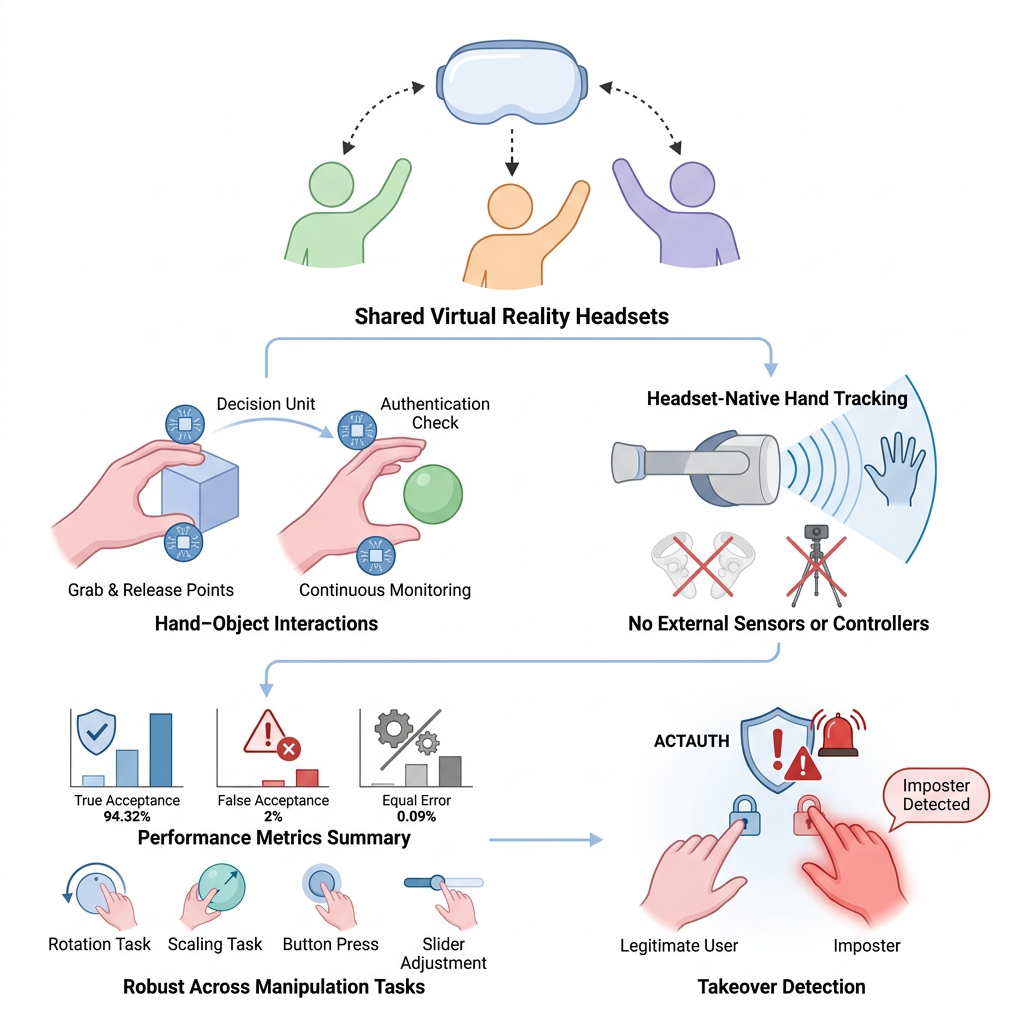
ACTAUTH: Interaction-Triggered, Continuous User Authentication for Controller-Free Virtual Reality
Accepted in IEEE International Conference on Cyber Security and Resilience (CSR) · 2026
ACTAUTH is a controller-free continuous user authentication framework for shared VR headsets that recognizes users from natural hand-object interactions on headset-native hand tracking, no controllers or external sensors required. Using grab-and-release events as decision units, a proof-of-concept on Meta Quest 3S achieves 94.32% true-acceptance at 2% FAR (0.09% EER) and detects 100% of simulated session takeovers within a single imposter interaction.
@inproceedings{actauth2026, title = {ACTAUTH: Interaction-Triggered, Continuous User Authentication for Controller-Free Virtual Reality}, author = {Li, Haoran and Achkar, Omar and Zouridakis, George and Fu, Xin and Lee, Kyu In}, booktitle = {IEEE International Conference on Cyber Security and Resilience (CSR)}, year = {2026}, note = {To appear} } -
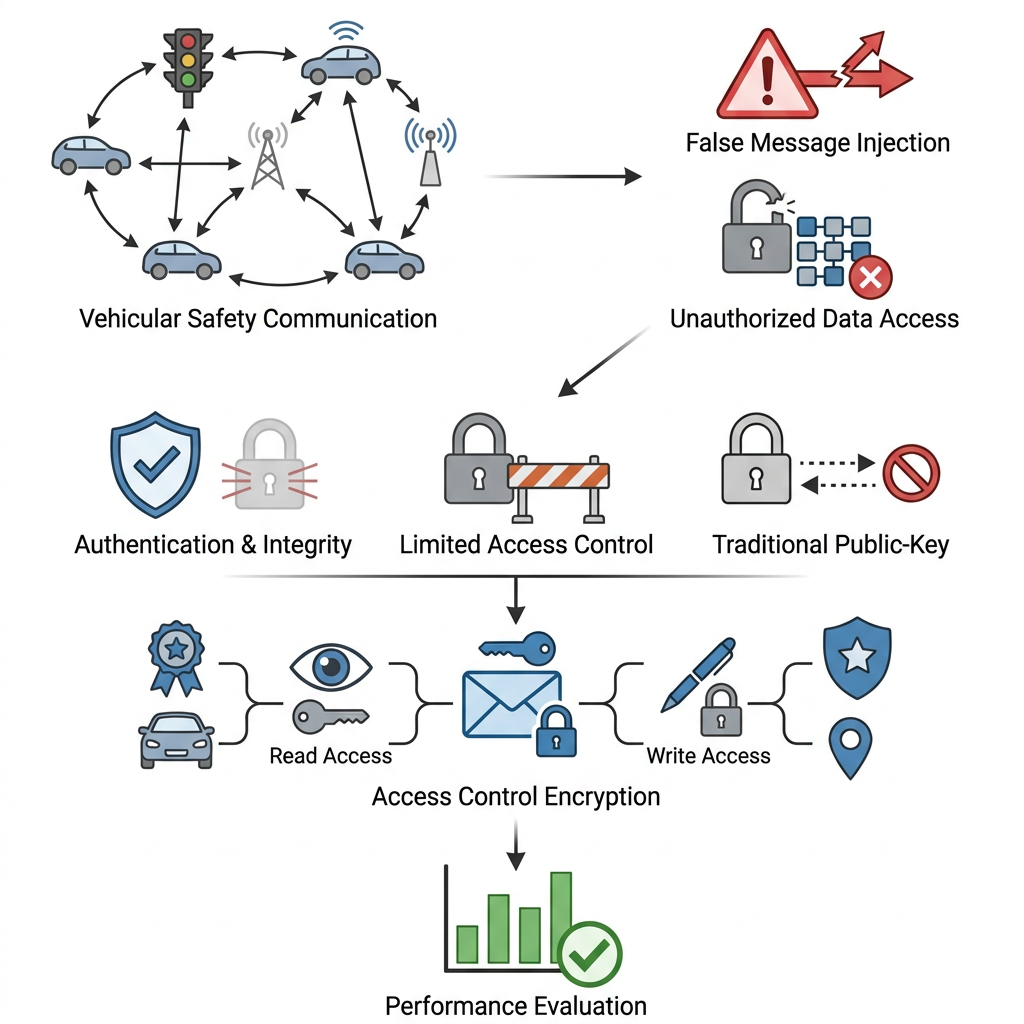
Securing the Lifeline: Enforcing Read and Write Access Control in Vehicular Safety Services
Accepted in IEEE International Conference on Cyber Security and Resilience (CSR) · 2026
A security mechanism for Internet-of-Vehicles (IoV) safety services that uses access control encryption to enforce both read (decrypt) and write (encrypt) policies on safety messages, going beyond traditional authentication/integrity to support fine-grained, contextual access by vehicle role, trust level, or proximity. Evaluation shows reasonable computational overhead, making the scheme practical for vehicular safety applications.
@inproceedings{lifeline2026, title = {Securing the Lifeline: Enforcing Read and Write Access Control in Vehicular Safety Services}, author = {Mollah, Muhammad Baqer and Zouridakis, George and Lee, Kyu In}, booktitle = {IEEE International Conference on Cyber Security and Resilience (CSR)}, year = {2026}, note = {To appear} }
// 2025
-
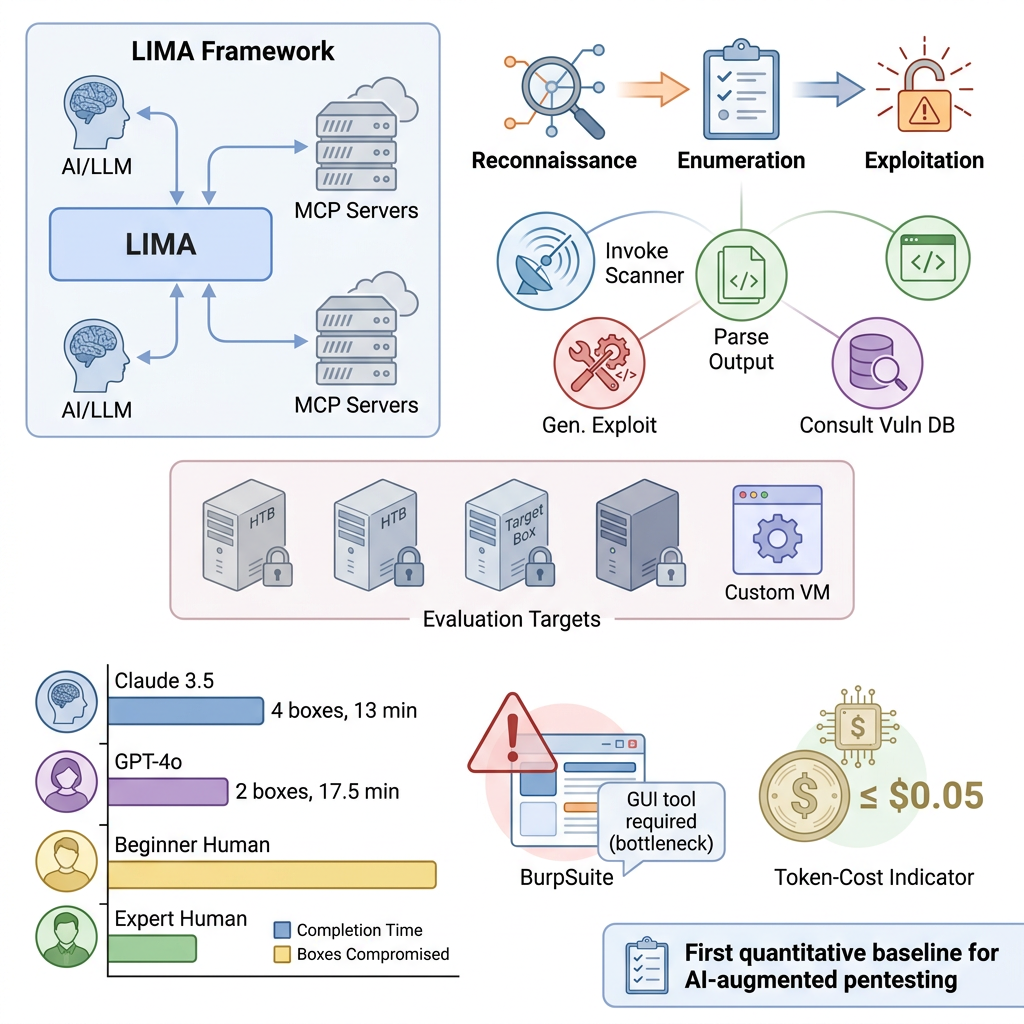
LIMA: Leveraging Large Language Models and MCP Servers for Initial Machine Access
IEEE International Conference on Future Machine Learning and Data Science (FMLDS) · 2025
A penetration-testing framework that pairs off-the-shelf LLMs with Model Context Protocol servers so the model can autonomously perform reconnaissance, enumeration, and exploitation of an initial-access target. On HackTheBox machines Claude 3.5 finished four boxes in ~13 minutes (up to 2x faster than expert testers) at under $0.05 per run, providing the first quantitative baseline for AI-augmented penetration testing.
@inproceedings{lima2025, title = {LIMA: Leveraging Large Language Models and MCP Servers for Initial Machine Access}, author = {Saleem, Mohammad Ibrahim and Prabhakar, Sohan Simha and Harsha, Abhinav and Nagabhushan, Devayani and Conklin, William Arthur and Lee, Kyu In and Banerjee, Tania}, booktitle = {IEEE International Conference on Future Machine Learning and Data Science (FMLDS)}, year = {2025} } -

PARAVIRT: Userland Containers for Mobile Systems
IEEE International Conference on Intelligent Mobile Computing (IMC) · 2025
PARAVIRT is a userland containerization framework for mobile operating systems that isolates applications inside a standard runtime environment without requiring root privileges. An optimized paravirtualization-inspired syscall interface yields up to 2.5x faster disk writes and 4 to 5.9x higher network throughput than User Mode Linux, approaching the performance of full virtualization platforms.
@inproceedings{paravirt2025, title = {PARAVIRT: Userland Containers for Mobile Systems}, author = {Ahlgren, Isaac and Silva, Yasin N. and Chan-Tin, Eric and Thiruvathukal, George K. and Lee, Kyu In and Klingensmith, Neil}, booktitle = {IEEE International Conference on Intelligent Mobile Computing (IMC)}, year = {2025} } -
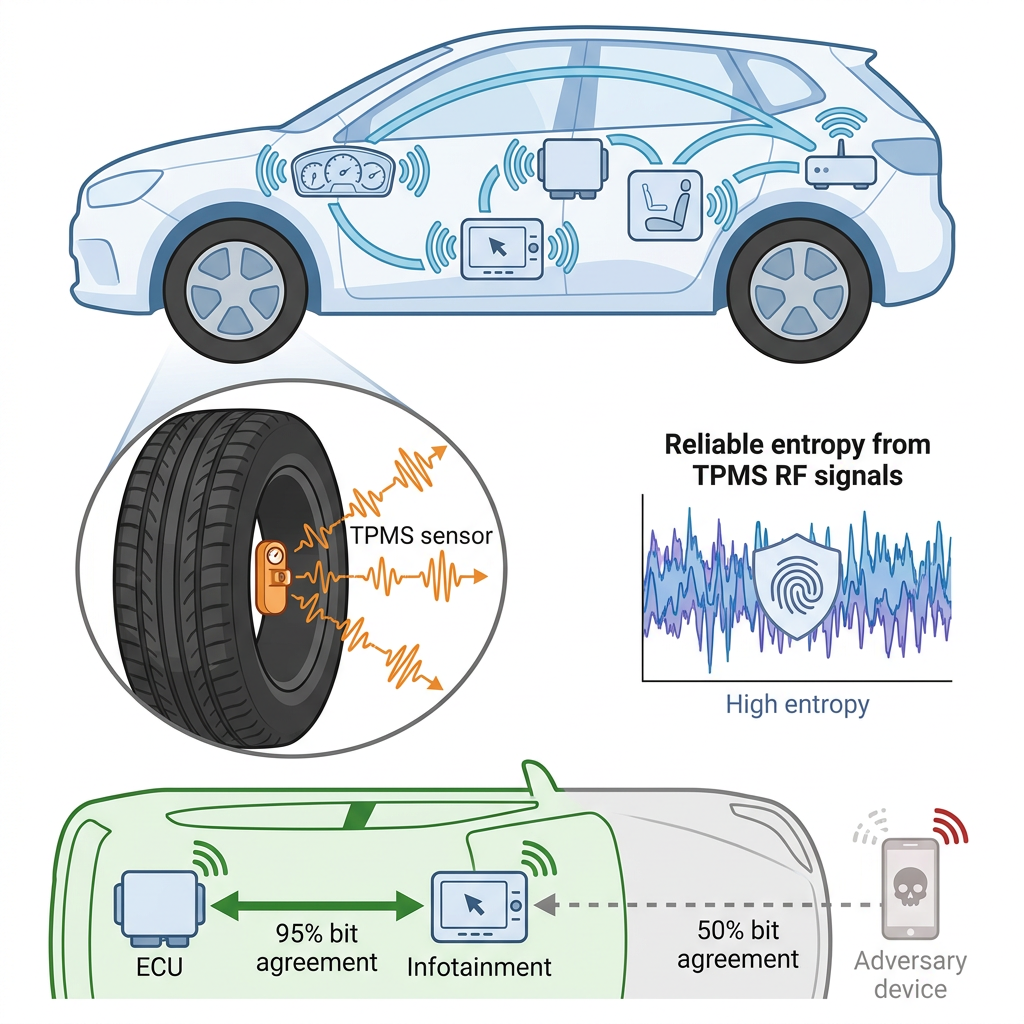
TPKey: Using TPMS Signals for Secure and Usable Intra-Vehicle Device Authentication
IEEE International Conference on Cyber Security and Resilience (CSR) · 2025
TPKEY is a zero-involvement authentication protocol that extracts high-entropy keys from a vehicle’s tire-pressure-monitoring-system (TPMS) RF signals, accessible only inside the cabin. It achieves 100% authentication success on legitimate devices, 0% false acceptance against adversaries, and 1.3-second key generation across varied driving conditions.
@inproceedings{tpkey2025, title = {TPKey: Using TPMS Signals for Secure and Usable Intra-Vehicle Device Authentication}, author = {Achkar, Omar and Nissen, Larry and Raza, Shahryar and Shirsat, Rushikesh and Klingensmith, Neil and Zouridakis, George and Lee, Kyu In}, booktitle = {IEEE International Conference on Cyber Security and Resilience (CSR)}, year = {2025} } -
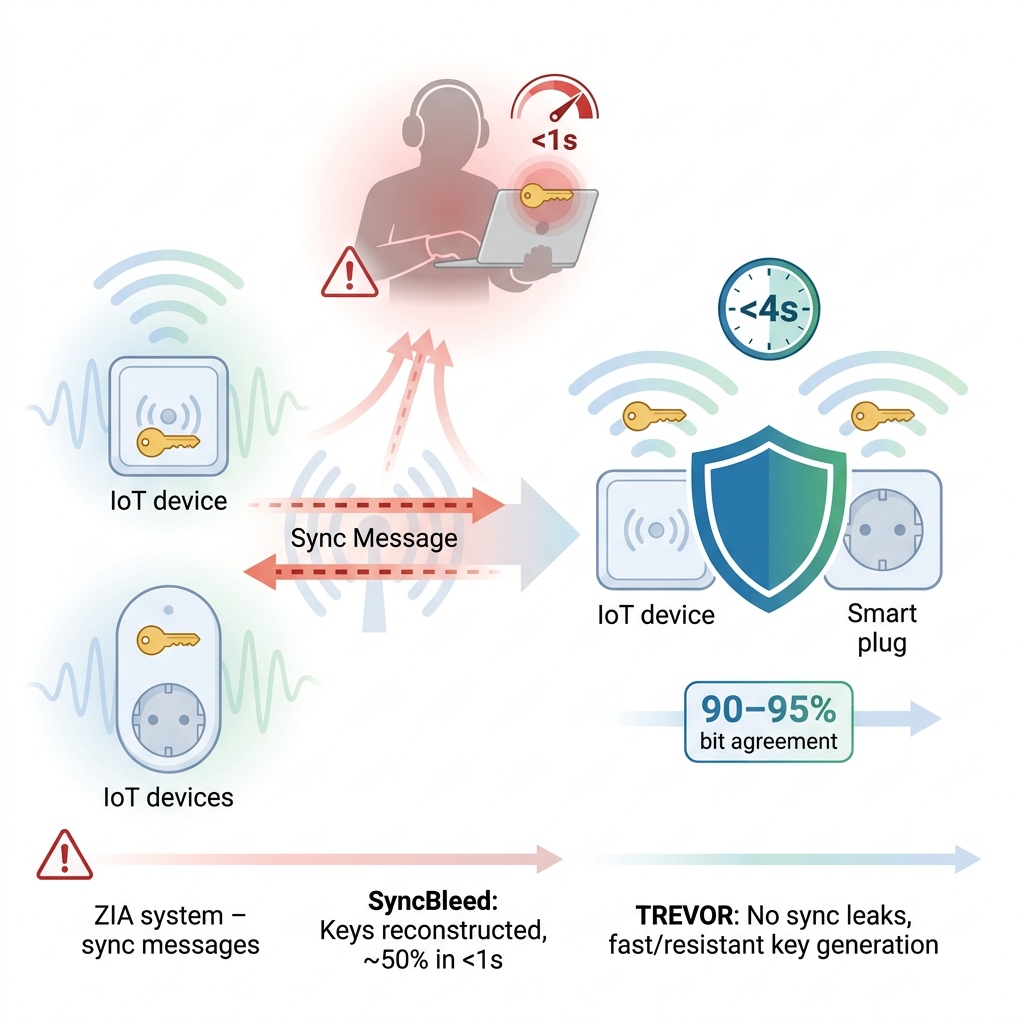
Not-so-Secret Authentication: The SyncBleed Attacks and Defenses for Zero-Involvement Authentication Systems
IEEE International Conference on Cyber Security and Resilience (CSR) · 2025
Identifies SyncBleed, a passive attack on zero-involvement authentication systems that exploits synchronization messages exchanged over public wireless channels, recovering ~50% of generated keys in under one second. Introduces TREVOR (Time-shift REsistant VEctor ExtractOR), which produces nearly identical bit sequences from environmental signals with no synchronization exchange and 90-95% bit agreement, fully resisting SyncBleed.
@inproceedings{syncbleed2025, title = {Not-so-Secret Authentication: The SyncBleed Attacks and Defenses for Zero-Involvement Authentication Systems}, author = {Ahlgren, Isaac and Shirsat, Rushikesh and Achkar, Omar and Thiruvathukal, George K. and Lee, Kyu In and Klingensmith, Neil}, booktitle = {IEEE International Conference on Cyber Security and Resilience (CSR)}, year = {2025} } -
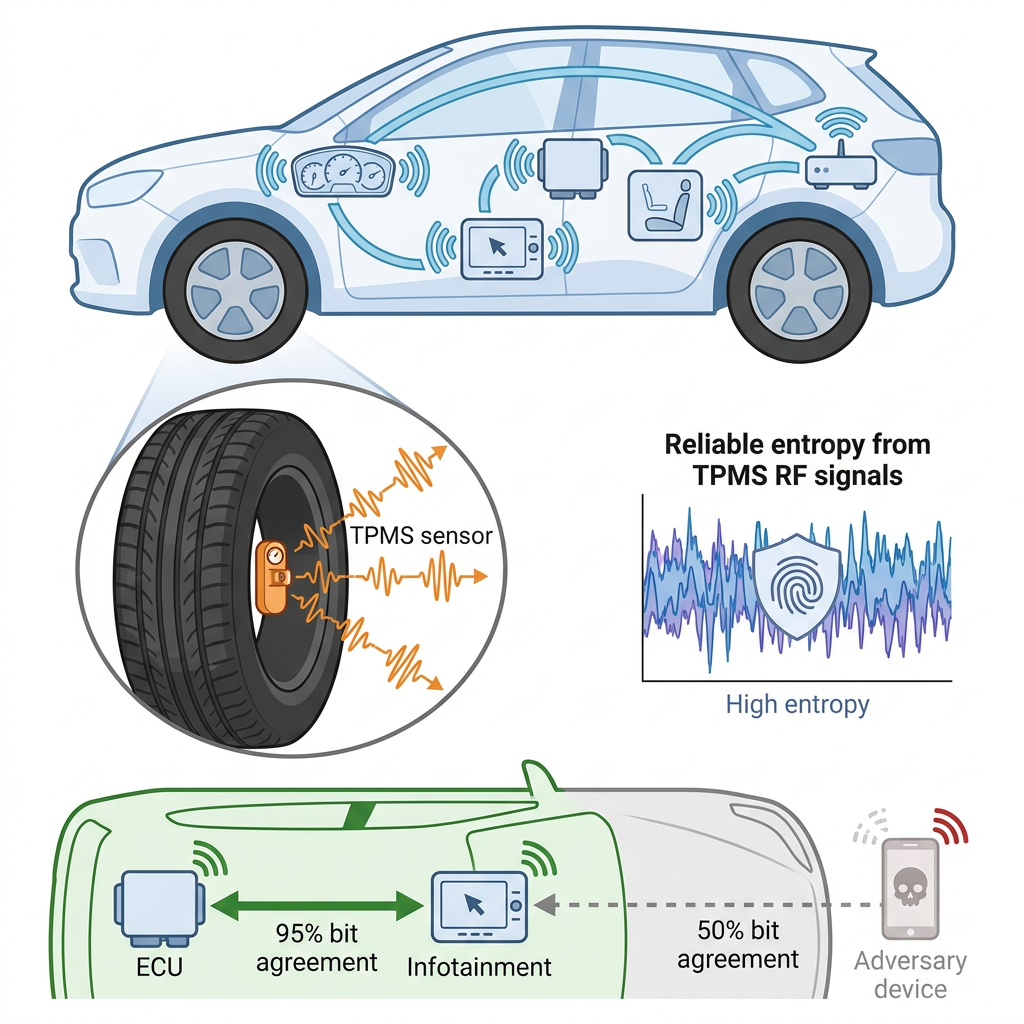
In-Progress: Exploring Tire Pressure Monitoring Systems (TPMS) for Secure Key Generation for Intra-Vehicular Device Authentication
★ Best Short Paper, SecureTrans Workshop
IEEE Symposium on Security and Privacy Workshops (SPW) · 2025
Early exploration of using Tire Pressure Monitoring System (TPMS) RF transmissions as a source of environmental randomness for automotive authentication. Experiments show 95% bit-agreement among legitimate in-cabin devices versus 50% for external adversaries, suggesting TPMS-based zero-interaction authentication is a practical direction for modern vehicles.
@inproceedings{inprogresstpms2025, title = {In-Progress: Exploring Tire Pressure Monitoring Systems (TPMS) for Secure Key Generation for Intra-Vehicular Device Authentication}, author = {Achkar, Omar and Raza, Shahryar and McAvoy, James and Shirsat, Rushikesh and Klingensmith, Neil and Lee, Kyu In}, booktitle = {IEEE Symposium on Security and Privacy Workshops (SPW)}, year = {2025} }
// 2024
-
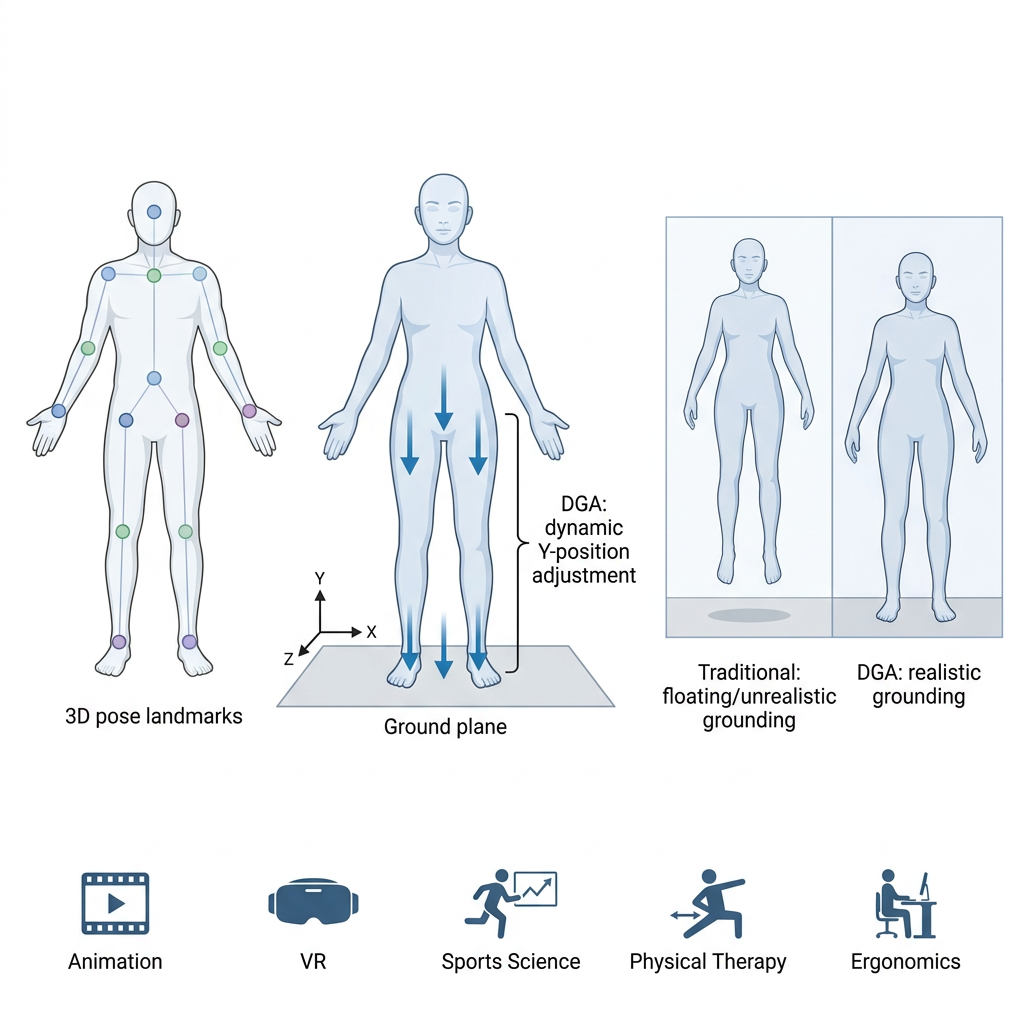
Ground-Relative Positioning in 3D Pose Estimation: A Novel Approach for Real-World Alignment of Skeleton Data
IEEE International Conference on Ubiquitous Robots (UR) · 2024
Introduces Dynamic Ground Alignment (DGA), a 3D pose-estimation algorithm built on Mediapipe Pose that uses body-centered 3D landmarks to align digital characters with the ground plane in virtual environments. Improves character grounding for animation, virtual reality, sports science, physical therapy, and ergonomic studies.
@inproceedings{groundrelative2024, title = {Ground-Relative Positioning in 3D Pose Estimation: A Novel Approach for Real-World Alignment of Skeleton Data}, author = {Kim, Myeongseop and Taehyeon, Kim and Oh, Jean and Lee, Kyu In and Lee, Kyung-Taek}, booktitle = {IEEE International Conference on Ubiquitous Robots (UR)}, year = {2024} } -
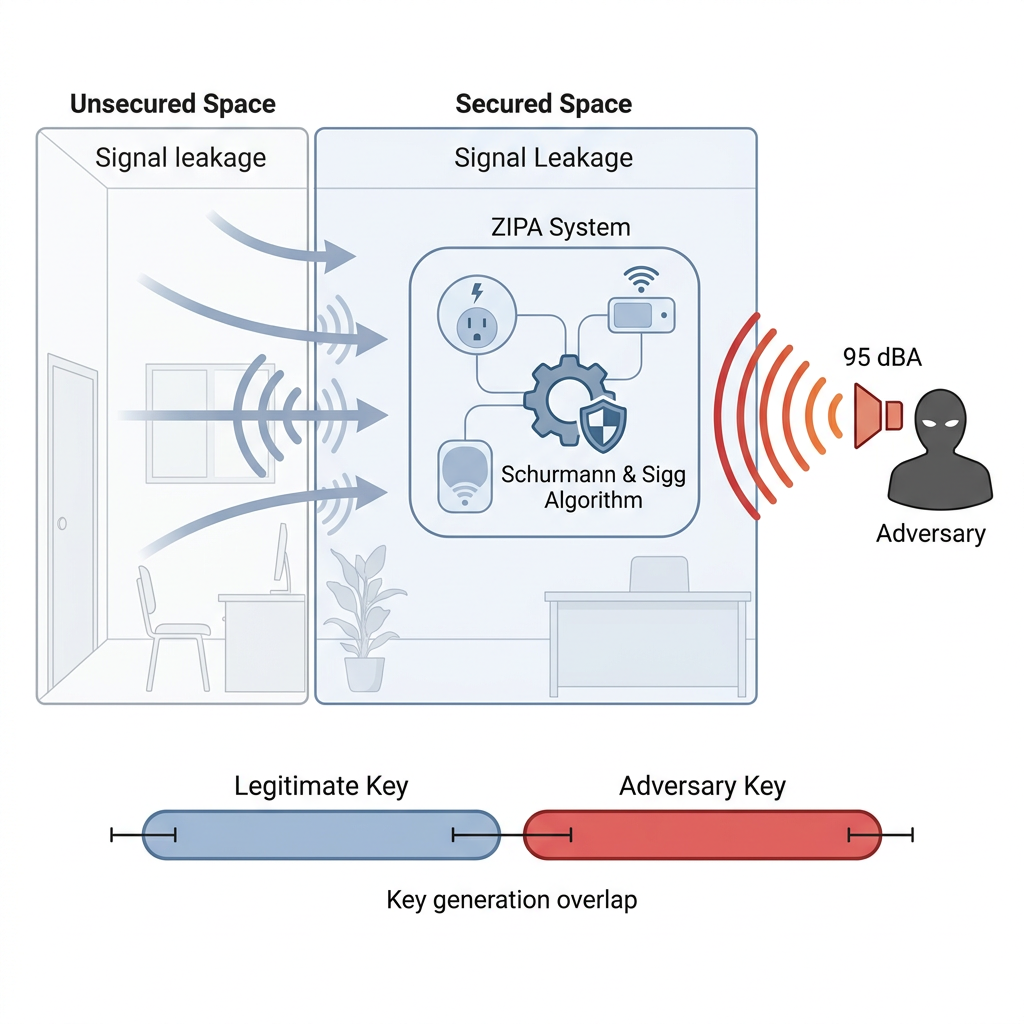
A Signal Injection Attack Against Zero Involvement Pairing and Authentication for the Internet of Things
ACM/IEEE Workshop on Design Automation for CPS and IoT (DESTION) · 2024
Demonstrates the first successful signal-injection attack on a zero-involvement pairing and authentication (ZIPA) system, exploiting environmental signal leakage from unsecured spaces into secured ones. The attacker’s keys at 95 dBA fall within the standard error of the legitimate device, breaking the implicit physical-isolation assumption of popular ZIPA algorithms.
@inproceedings{injection2024, title = {A Signal Injection Attack Against Zero Involvement Pairing and Authentication for the Internet of Things}, author = {Ahlgren, Isaac and West, Jack and Lee, Kyuin and Thiruvathukal, George K. and Klingensmith, Neil}, booktitle = {ACM/IEEE Workshop on Design Automation for CPS and IoT (DESTION)}, year = {2024} }
// 2022
-
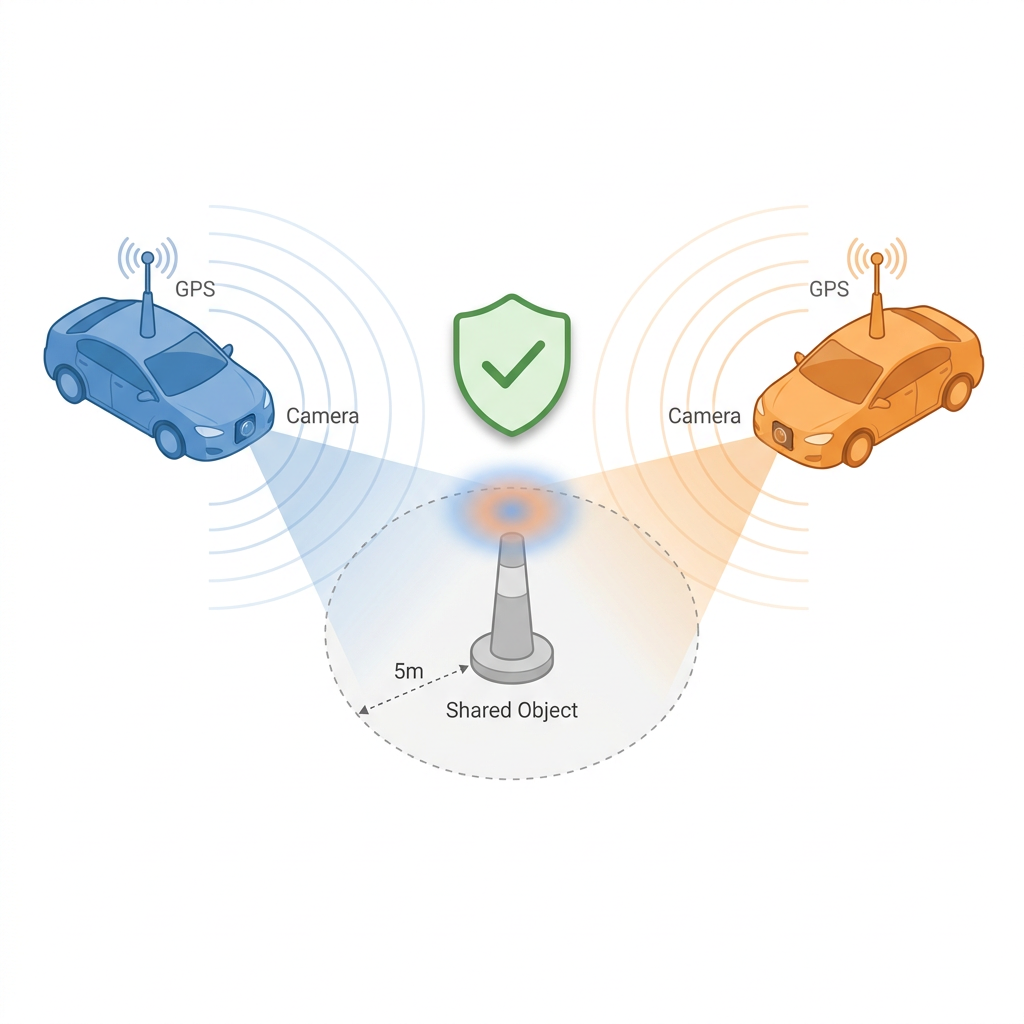
Establishing Trust in Vehicle-to-Vehicle Coordination: A Sensor Fusion Approach
IEEE Workshop on Data-Driven and Intelligent Cyber-Physical Systems (DI-CPS) · 2022
A sensor-fusion approach to V2V trust establishment that combines GPS and visual data so an autonomous vehicle can verify a peer is physically nearby, no infrastructure or third-party root of trust required. Preliminary experiments achieve >80% successful pairing of two legitimate vehicles observing the same object within 5 meters of error.
@inproceedings{v2v2022, title = {Establishing Trust in Vehicle-to-Vehicle Coordination: A Sensor Fusion Approach}, author = {Veselsky, Jakob and West, Jack and Ahlgren, Isaac and Goel, Abhinav and Jiang, Wenxin and Lee, Kyuin and Kim, Younghyun and Davis, James and Thiruvathukal, George K. and Klingensmith, Neil}, booktitle = {IEEE Workshop on Data-Driven and Intelligent Cyber-Physical Systems (DI-CPS)}, pages = {7--13}, year = {2022} } -
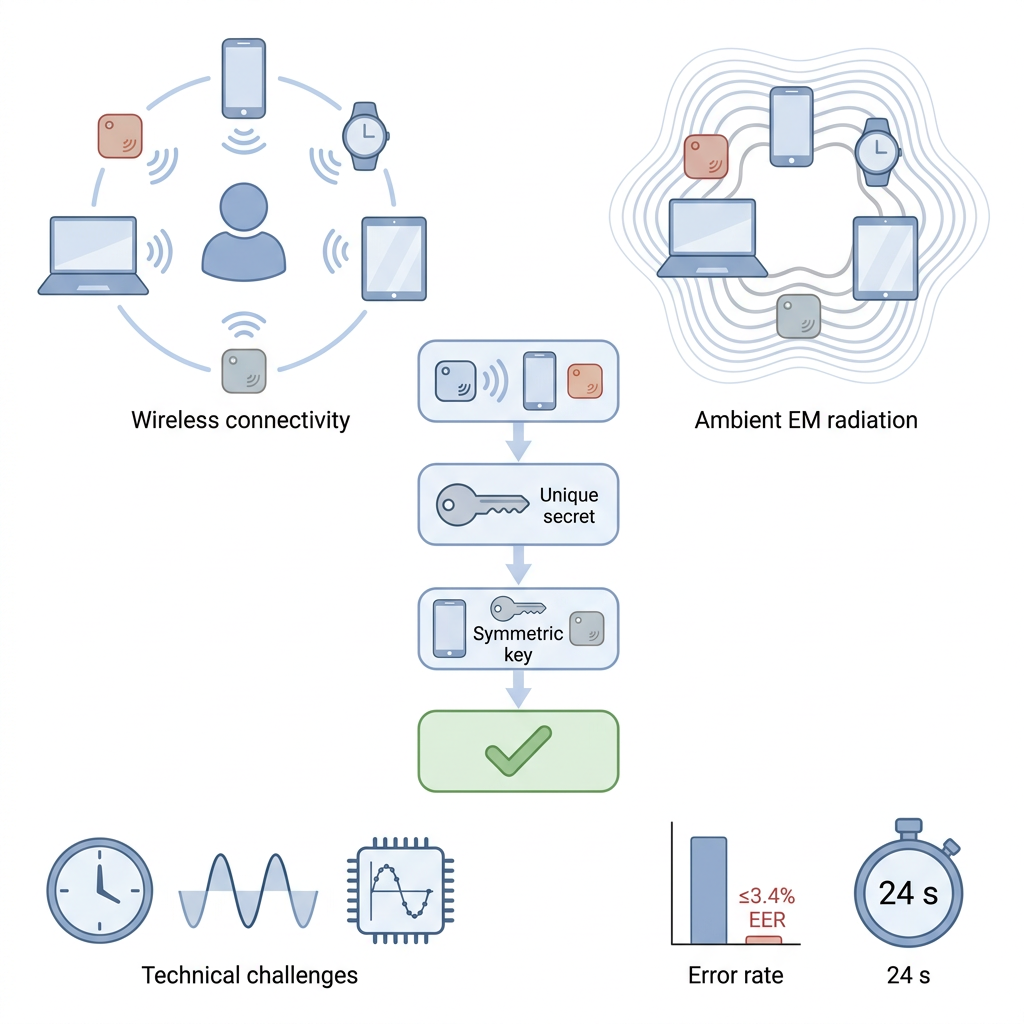
AeroKey: Using Ambient Electromagnetic Radiation for Secure and Usable Wireless Device Authentication
Proceedings of the ACM on Interactive, Mobile, Wearable and Ubiquitous Technologies (IMWUT) · 2022
AeroKey is an over-the-air device authentication scheme that derives spatiotemporally unique secrets from ambient electromagnetic radiation, allowing co-located low-cost MCU devices to autonomously establish a shared symmetric key with no user involvement. Real-world experiments report equal-error rates of 3.4% or below and authentication times as low as 24 seconds.
@article{aerokey2022, title = {AeroKey: Using Ambient Electromagnetic Radiation for Secure and Usable Wireless Device Authentication}, author = {Lee, Kyuin and Yang, Yucheng and Prabhune, Omkar and Chithra, Aishwarya Lekshmi and West, Jack and Fawaz, Kassem and Klingensmith, Neil and Banerjee, Suman and Kim, Younghyun}, journal = {Proceedings of the ACM on Interactive, Mobile, Wearable and Ubiquitous Technologies (IMWUT)}, volume = {6}, number = {1}, year = {2022} } -
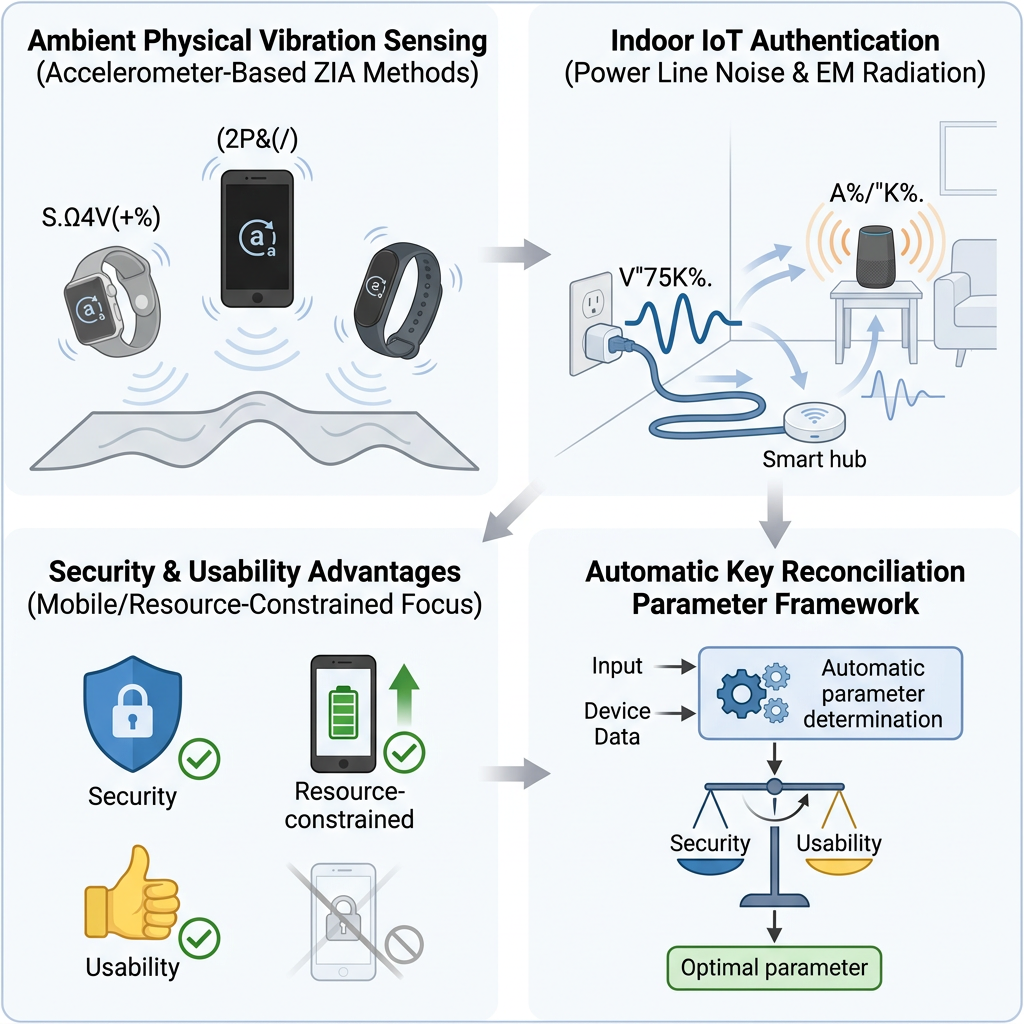
Secure, Usable and Practical Authentication for the Internet of Things
PhD Dissertation, University of Wisconsin-Madison · 2022
PhD dissertation on secure, usable, and practical authentication for IoT devices. Develops zero-involvement pairing and authentication methods that derive shared keys from co-located physical context (power-line noise, ambient electromagnetic radiation, vibration), with new randomness distillers, threat models for context-based key extraction, and field deployments across smart-home, vehicular, and wearable settings.
@phdthesis{leedissertation2022, title = {Secure, Usable and Practical Authentication for the Internet of Things}, author = {Lee, Kyuin}, school = {University of Wisconsin--Madison}, year = {2022} }
// 2021
-
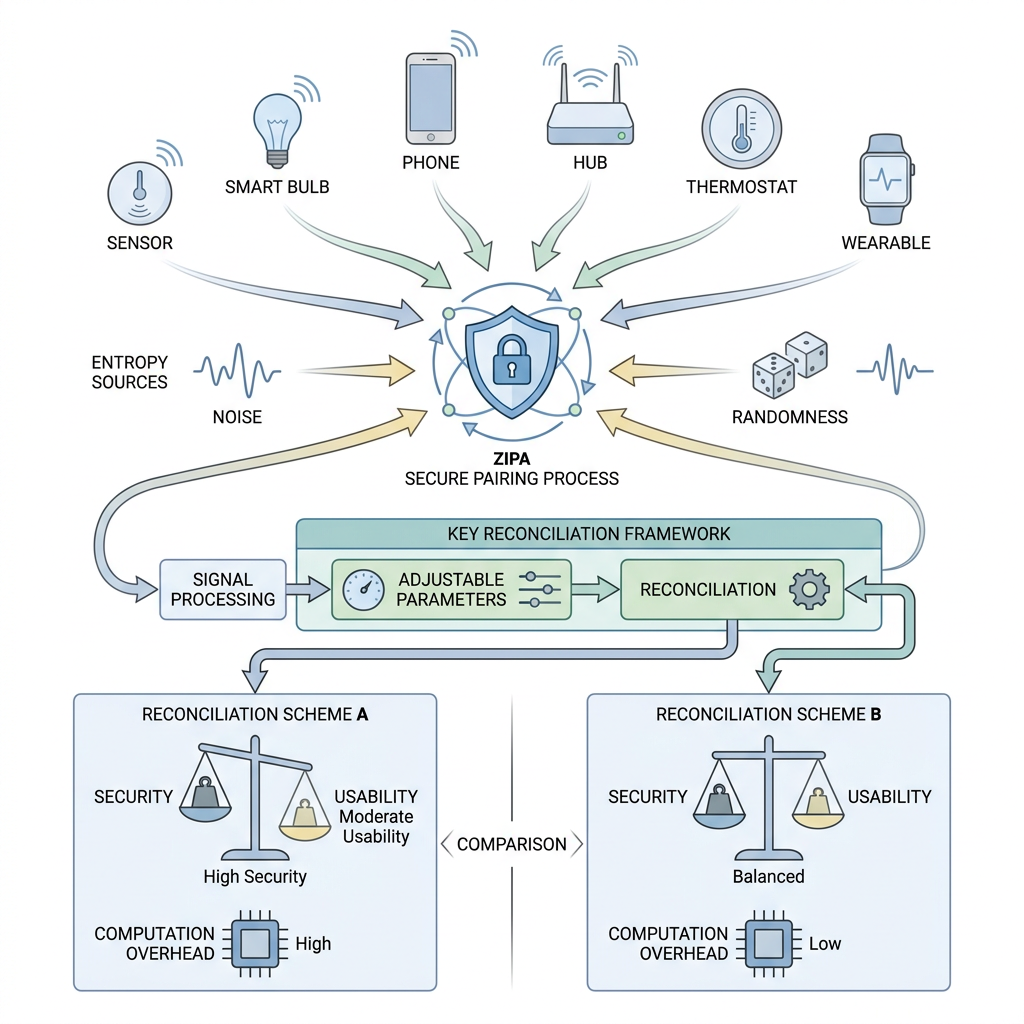
Balancing Security and Usability of Zero-interaction Pairing and Authentication for the Internet-of-Things
ACM Workshop on CPS & IoT Security and Privacy (CPSIoTSec) · 2021
Surveys the security-vs-usability trade-off in zero-interaction pairing and authentication (ZIPA) for IoT, and proposes a generic key-reconciliation framework parameterized by a user-given authentication range. Compares the two most common reconciliation schemes for security, usability, and computation overhead.
@inproceedings{balancing2021, title = {Balancing Security and Usability of Zero-interaction Pairing and Authentication for the Internet-of-Things}, author = {Lee, Kyuin and Kim, Younghyun}, booktitle = {ACM Workshop on CPS \& IoT Security and Privacy (CPSIoTSec)}, pages = {29--34}, year = {2021} } -
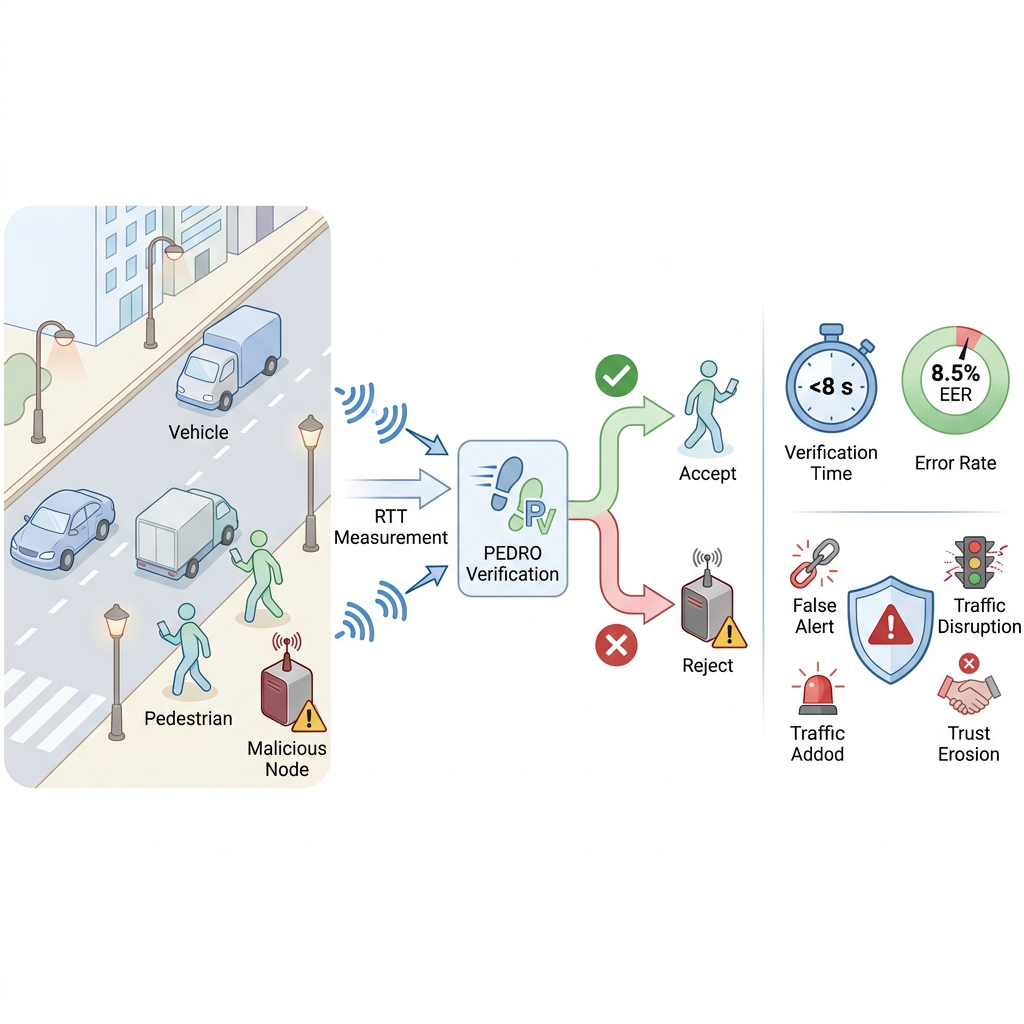
PEDRO: Secure Pedestrian Mobility Verification in V2P Communication using COTS Mobile Devices
ACM Workshop on CPS & IoT Security and Privacy (CPSIoTSec) · 2021
PEDRO verifies that a V2P node claiming to be a pedestrian is actually a co-located mobile device, using round-trip wireless timing between vehicles and commodity pedestrian devices to admit moving devices and reject static (likely remote) malicious ones. Verification runs in under 8 seconds with an 8.5% Equal Error Rate in regular road environments. (* Equal contribution by Yang and Lee.)
@inproceedings{pedro2021, title = {PEDRO: Secure Pedestrian Mobility Verification in V2P Communication using COTS Mobile Devices}, author = {Yang, Yucheng and Lee, Kyuin and Kim, Younghyun and Fawaz, Kassem}, booktitle = {ACM Workshop on CPS \& IoT Security and Privacy (CPSIoTSec)}, pages = {41--46}, year = {2021} } -
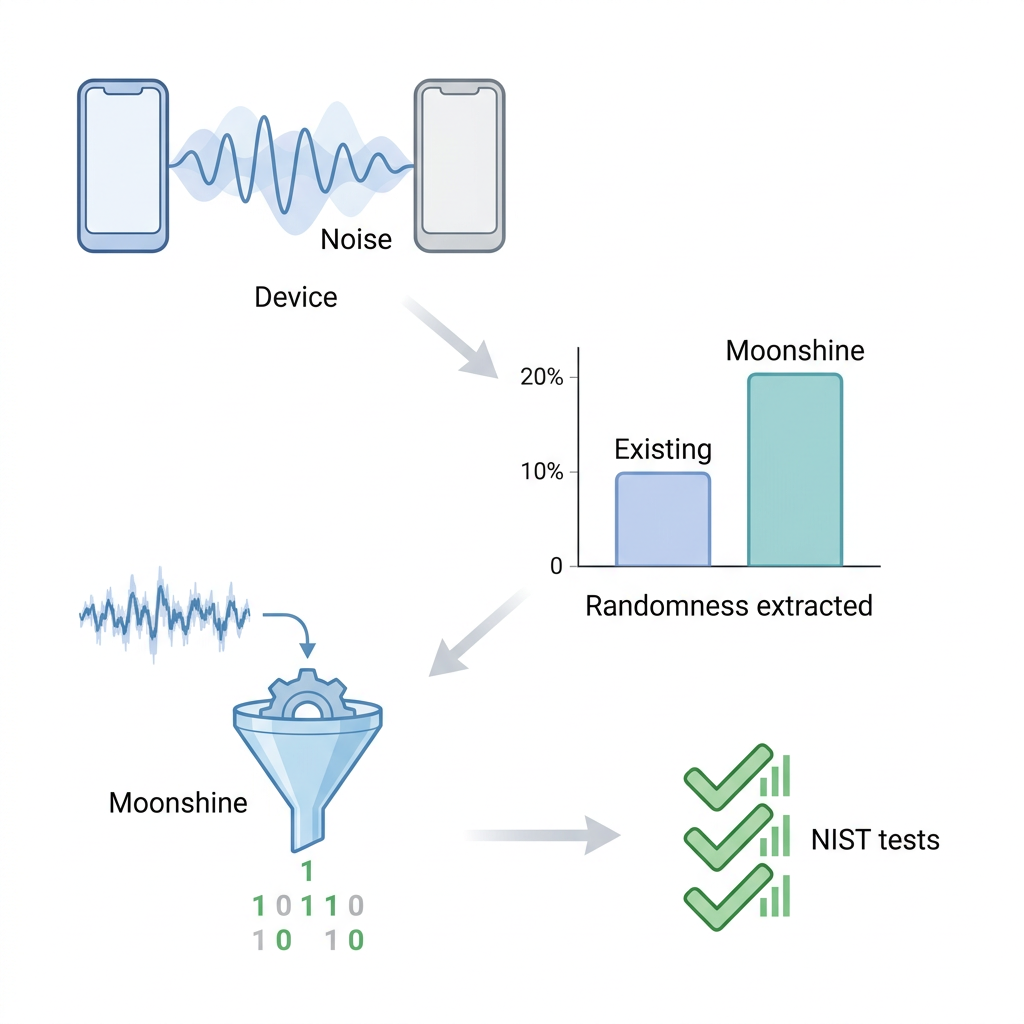
Moonshine: An Online Randomness Distiller for Zero-Involvement Authentication
ACM/IEEE International Conference on Information Processing in Sensor Networks (IPSN) · 2021
Studies the information-theoretic capacity of context-based key extraction and shows that commonly used bit extractors recover only ~10% of the available randomness from environmental noise. Moonshine is a randomness distiller that nearly doubles key quality on the NIST test suite using real key-extraction hardware.
@inproceedings{moonshine2021, title = {Moonshine: An Online Randomness Distiller for Zero-Involvement Authentication}, author = {West, Jack and Lee, Kyuin and Banerjee, Suman and Kim, Younghyun and Thiruvathukal, George K. and Klingensmith, Neil}, booktitle = {ACM/IEEE International Conference on Information Processing in Sensor Networks (IPSN)}, pages = {93--105}, year = {2021} }
// 2020
-
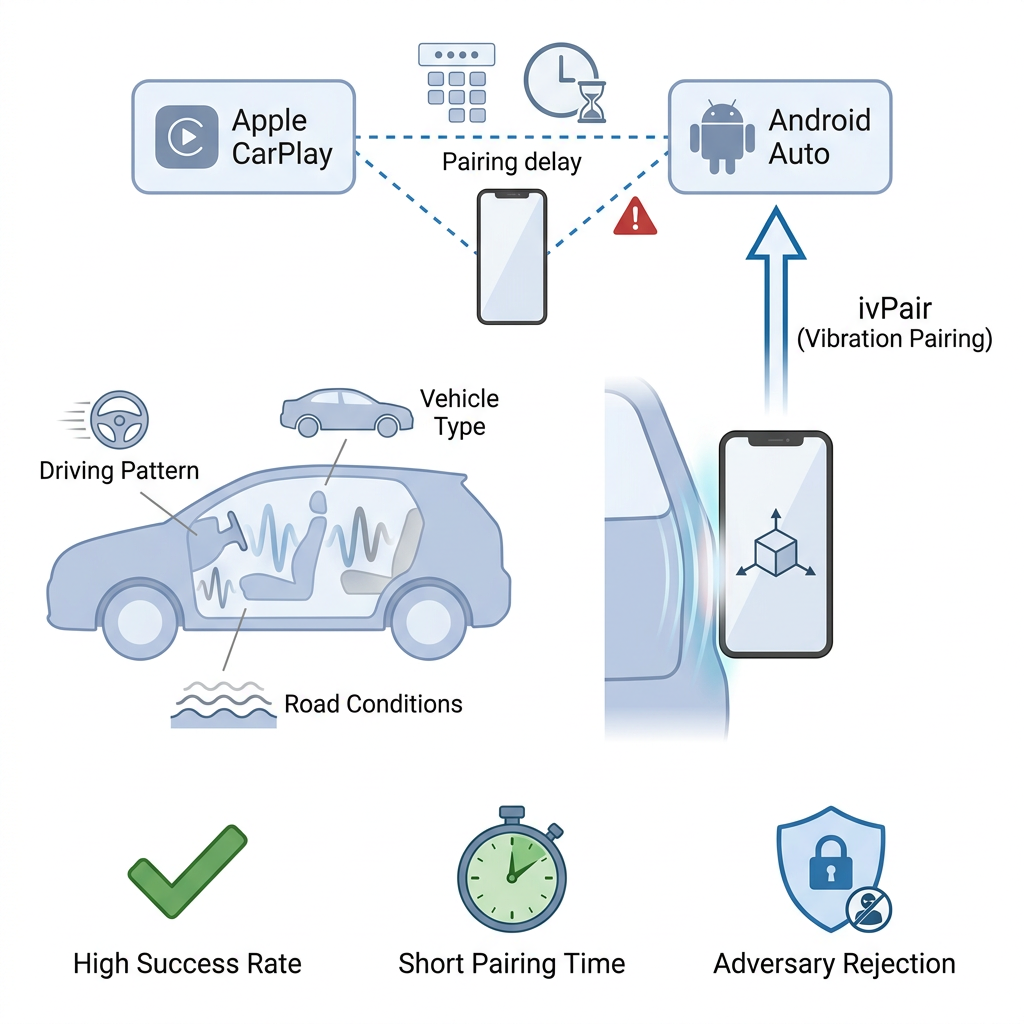
ivPair: Context-Based Fast Intra-Vehicle Device Pairing for Secure Wireless Connectivity
ACM Conference on Security and Privacy in Wireless and Mobile Networks (WiSec) · 2020
ivPair pairs a phone with a vehicle’s infotainment system by extracting an identical pin from the cabin’s vibration response, driven by driver behavior, vehicle type, and road conditions. Experiments across realistic driving conditions show high in-cabin pairing success and effective rejection of proximate adversaries.
@inproceedings{ivpair2020, title = {ivPair: Context-Based Fast Intra-Vehicle Device Pairing for Secure Wireless Connectivity}, author = {Lee, Kyuin and Klingensmith, Neil and He, Dong and Banerjee, Suman and Kim, Younghyun}, booktitle = {ACM Conference on Security and Privacy in Wireless and Mobile Networks (WiSec)}, pages = {25--30}, year = {2020} } -
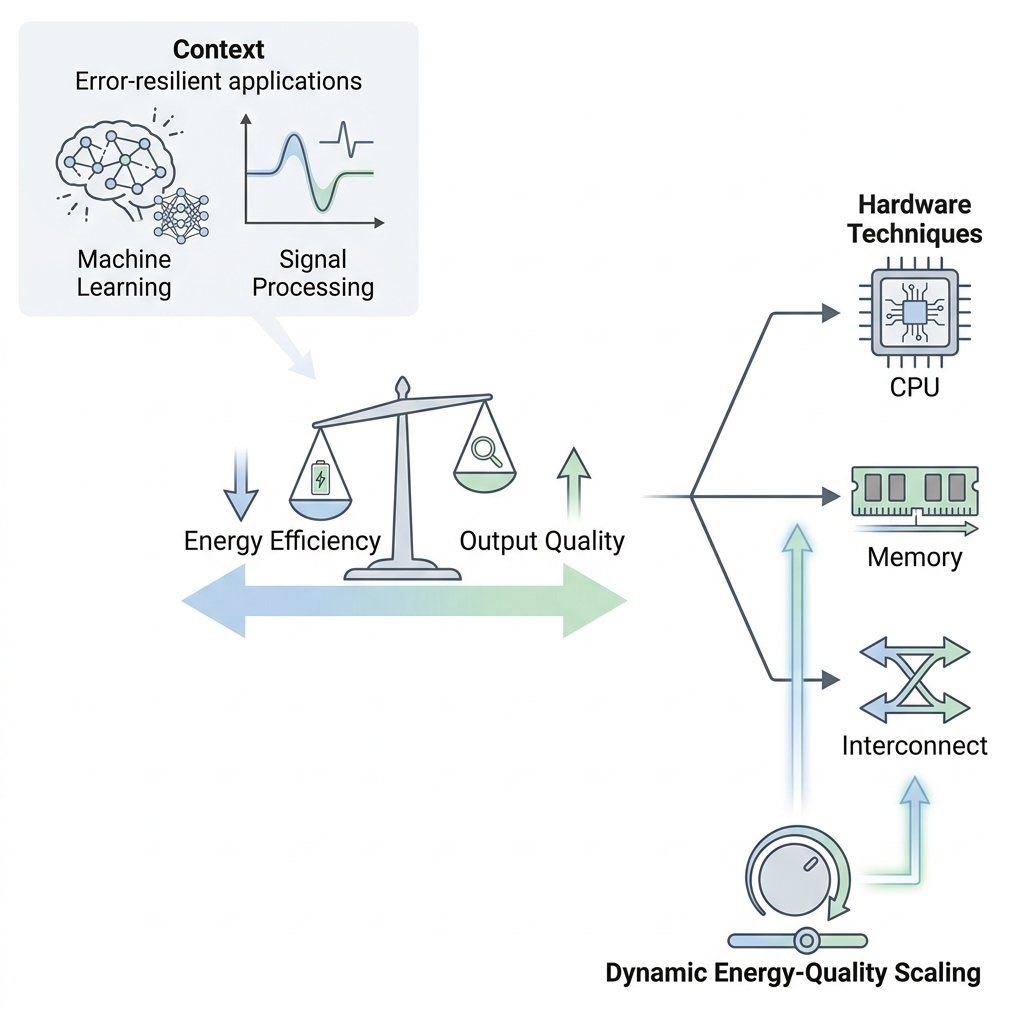
Approximate Hardware Techniques for Energy-Quality Scaling Across the System
IEIE/IEEE International Conference on Electronics, Information, and Communication (ICEIC) · 2020
A taxonomy of approximate-hardware techniques that trade output quality for energy efficiency across processors and logic, memory, I/O, and interconnects. The work classifies techniques by target subsystem and by support for runtime energy-quality scaling.
@inproceedings{approx2020, title = {Approximate Hardware Techniques for Energy-Quality Scaling Across the System}, author = {Kim, Younghyun and San Miguel, Joshua and Behroozi, Setareh and Chen, Tianen and Lee, Kyuin and Lee, Yongwoo and Li, Jingjie and Wu, Di}, booktitle = {IEIE/IEEE International Conference on Electronics, Information, and Communication (ICEIC)}, pages = {1--5}, year = {2020} }
// 2019
-
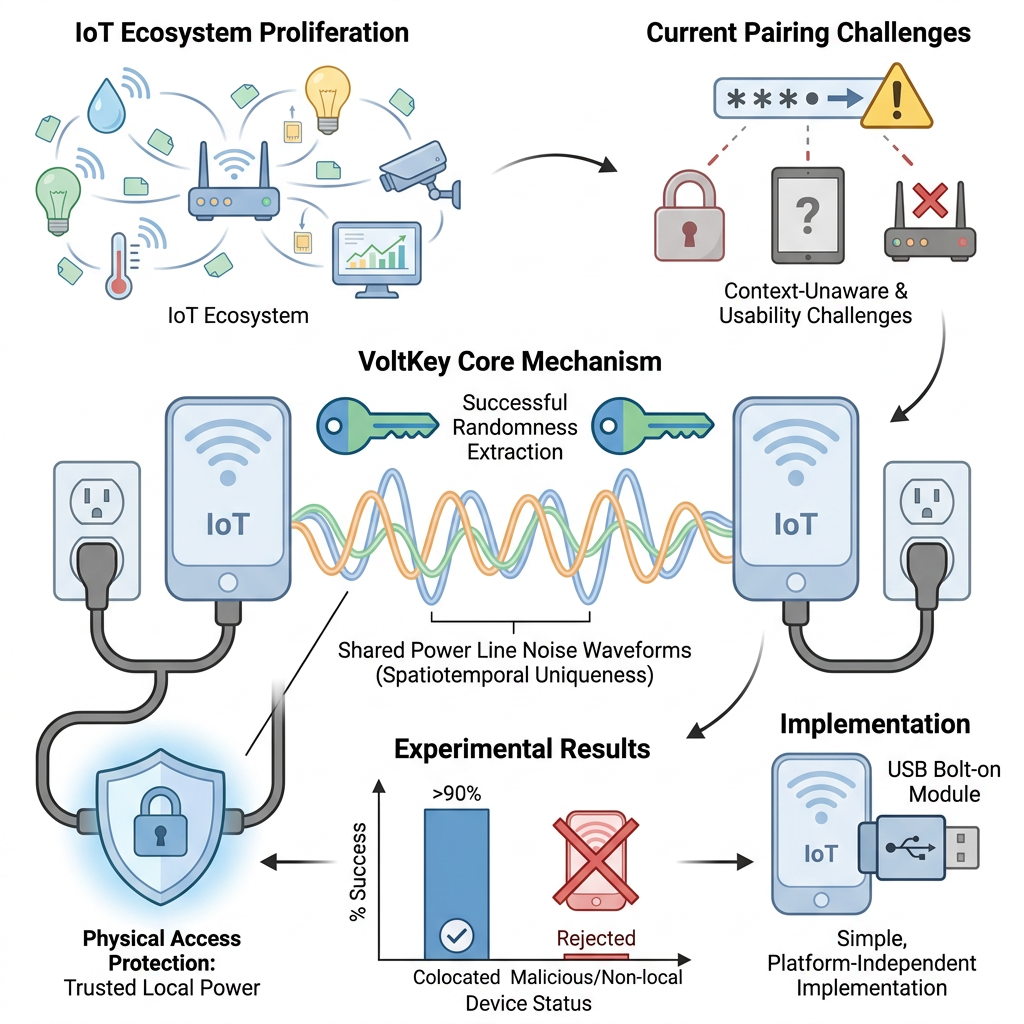
VoltKey: Continuous Secret Key Generation Based on Power Line Noise for Zero-Involvement Pairing and Authentication
Proceedings of the ACM on Interactive, Mobile, Wearable and Ubiquitous Technologies (IMWUT) · 2019
VoltKey continuously derives shared secret keys for co-located devices from the spatiotemporally unique noise on a local power line. Deployable as a USB-power add-on for IoT devices and access points, it achieves over 90% pairing success while rejecting devices on nearby (but separate) power lines.
@article{voltkey2019, title = {VoltKey: Continuous Secret Key Generation Based on Power Line Noise for Zero-Involvement Pairing and Authentication}, author = {Lee, Kyuin and Klingensmith, Neil and Banerjee, Suman and Kim, Younghyun}, journal = {Proceedings of the ACM on Interactive, Mobile, Wearable and Ubiquitous Technologies (IMWUT)}, volume = {3}, number = {3}, pages = {93:1--93:26}, year = {2019} }
// 2018
-
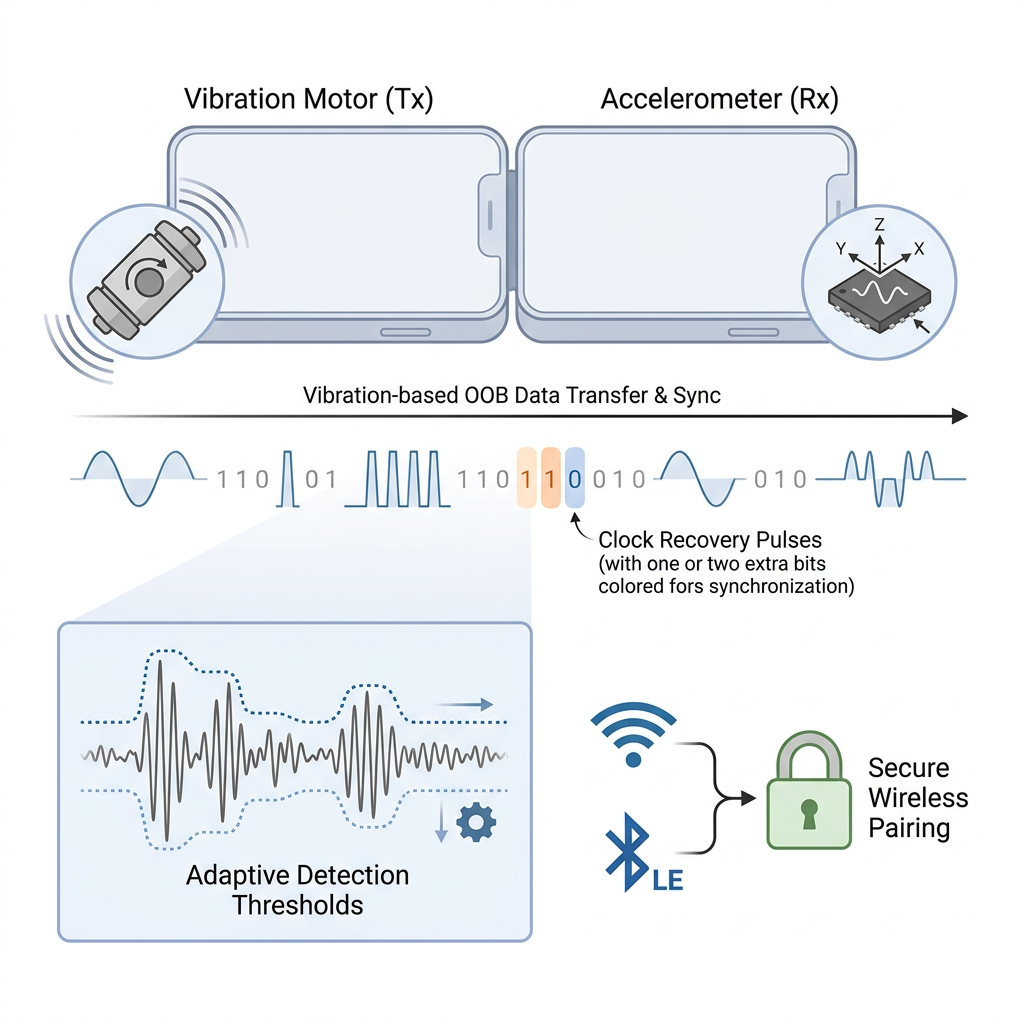
SyncVibe: Fast and Secure Device Pairing through Physical Vibration on Commodity Smartphones
IEEE International Conference on Computer Design (ICCD) · 2018
SyncVibe is an out-of-band pairing channel that uses a phone’s vibration motor and accelerometer to transmit pairing data through direct device contact. A vibration clock-recovery technique maintains synchronization across varied noise and transmission media, enabling fast, secure, high-bandwidth pairing without manual passkey entry.
@inproceedings{syncvibe2018, title = {SyncVibe: Fast and Secure Device Pairing through Physical Vibration on Commodity Smartphones}, author = {Lee, Kyuin and Raghunathan, Vijay and Raghunathan, Anand and Kim, Younghyun}, booktitle = {IEEE International Conference on Computer Design (ICCD)}, pages = {234--241}, year = {2018} }
No publications match this filter.
